When Redactions Un-Redact Themselves: The Cornwall Council GDPR Breach Explained
Cornwall Council exposed the personal data of 10 complainants — including home addresses, emails, and phone numbers — after redacted PDFs automaticall...
628 articles on privacy laws, security frameworks, and regulatory compliance.

Cornwall Council exposed the personal data of 10 complainants — including home addresses, emails, and phone numbers — after redacted PDFs automaticall...
Ofcom has issued a Confirmation Decision against 4chan for breaching three sections of the Online Safety Act 2023. 4chan's legal response involved a g...
A YC-backed compliance startup is accused of mass-producing fraudulent SOC 2, ISO 27001, HIPAA, and GDPR reports for hundreds of clients — and has now...

Spain's data protection authority (AEPD) has imposed a €950,000 fine on UK-based digital identity company Yoti for three distinct GDPR violations rela...

CISA has issued an urgent alert urging organizations to harden Microsoft Intune configurations following the devastating March 2026 cyberattack on med...

Senator Marsha Blackburn has released the discussion draft of the TRUMP AMERICA AI Act — a sweeping federal AI regulatory framework that would establi...
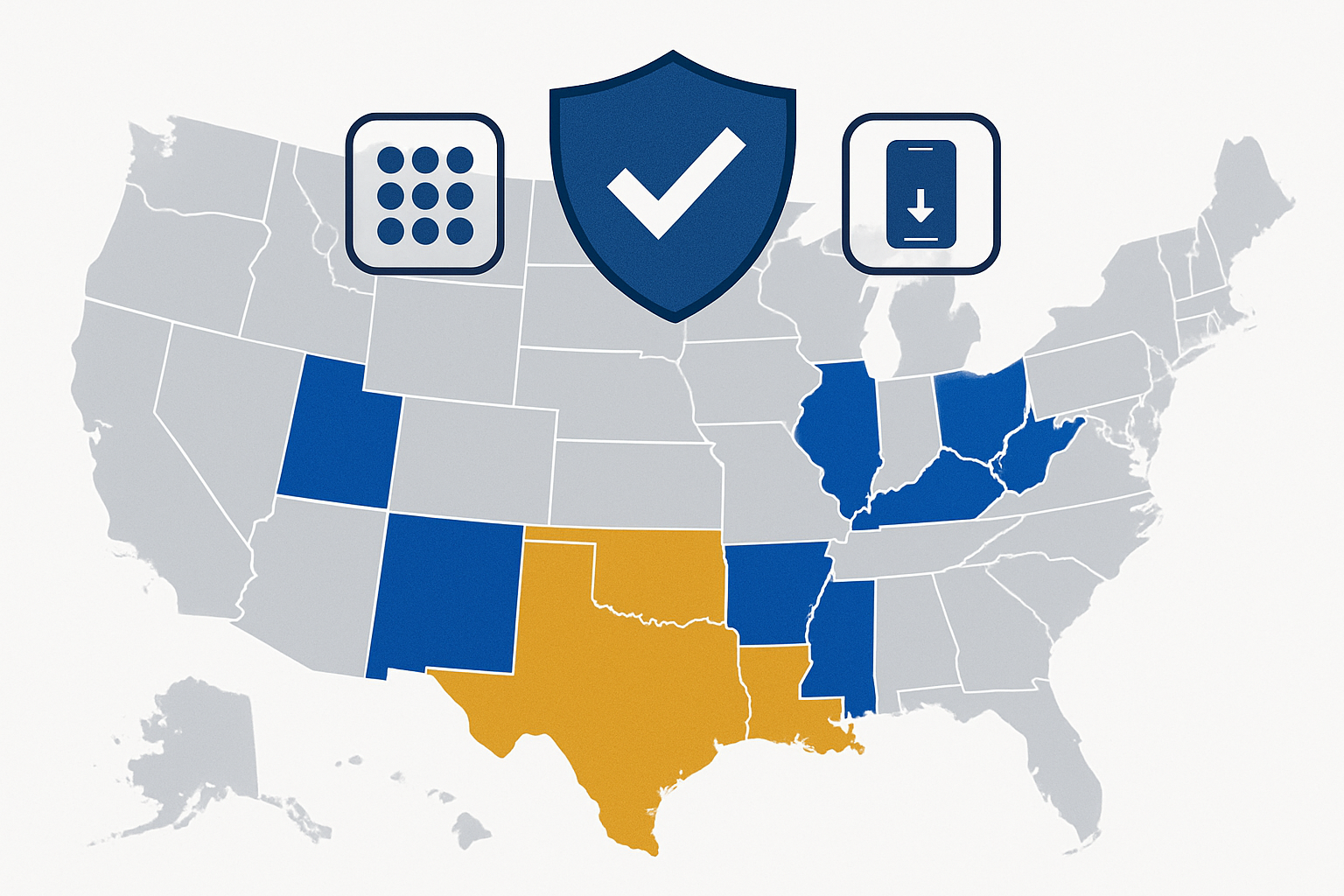
Alabama passes app store age verification law joining Louisiana, Texas, and Utah. Complete compliance guide for app developers and store operators....

Brazil's sweeping age verification law now requires all operating systems — including Linux — to verify user ages. Here's what compliance teams need t...

Vermont advances California Delete Act-style requirements for data brokers while New York embeds data broker provisions in budget bills. The regulator...

Three state privacy bills made significant moves this week. Alabama's comprehensive privacy law faces a tight deadline, Kentucky adds smart TV protect...

Texas Governor Greg Abbott has ordered a comprehensive cybersecurity review of Chinese-manufactured medical equipment in state-owned health facilities...

A South Carolina county paid $1.558 million to criminals impersonating a contractor via fraudulent wire transfer instructions. Analysis of how BEC att...
Showing 12 of 628 articles
Load More →